By Lerpong Intaraworrapath | September 7th ,2023
The version of the VMware Aria Operations for Logs (previously VMware vRealize Log Insight) program running on the remote system is 8.10.2. As a result, it is vulnerable to a remote code execution vulnerability caused by dangerous deserialization. An unauthenticated, a threat actor with network access to VMware Aria Operations for Logs can exploit this to execute arbitrary code as root.
https://www.vmware.com/security/advisories/VMSA-2023-0007.html
Solution
The issue has been fixed on VMware Aria Operations for Logs 8.12.
How can you update VMware Aria Operations for Logs from 8.10.2 to 8.12.0?
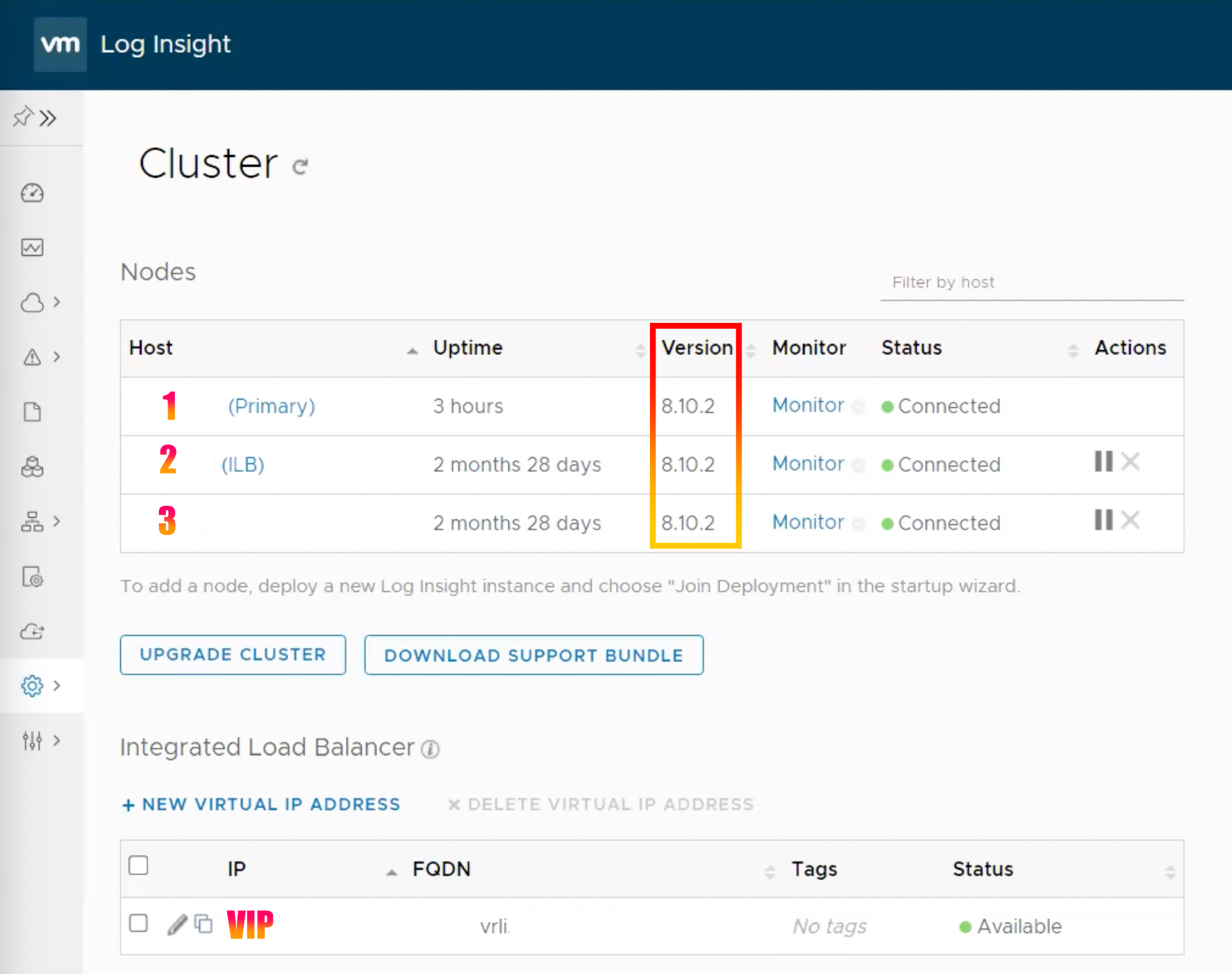
*In this article, we will upgrade a VMware Aria Operations for Logs cluster of three nodes.
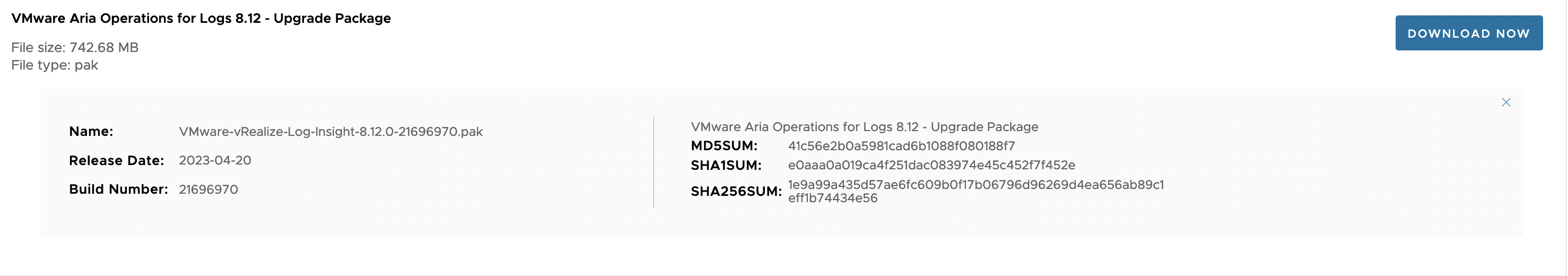
1.Download the VMware Aria Operations for Logs version 8.12.0 update file.
https://customerconnect.vmware.com/downloads/details?downloadGroup=OPLOGS-8120&productId=1419&rPId=103833
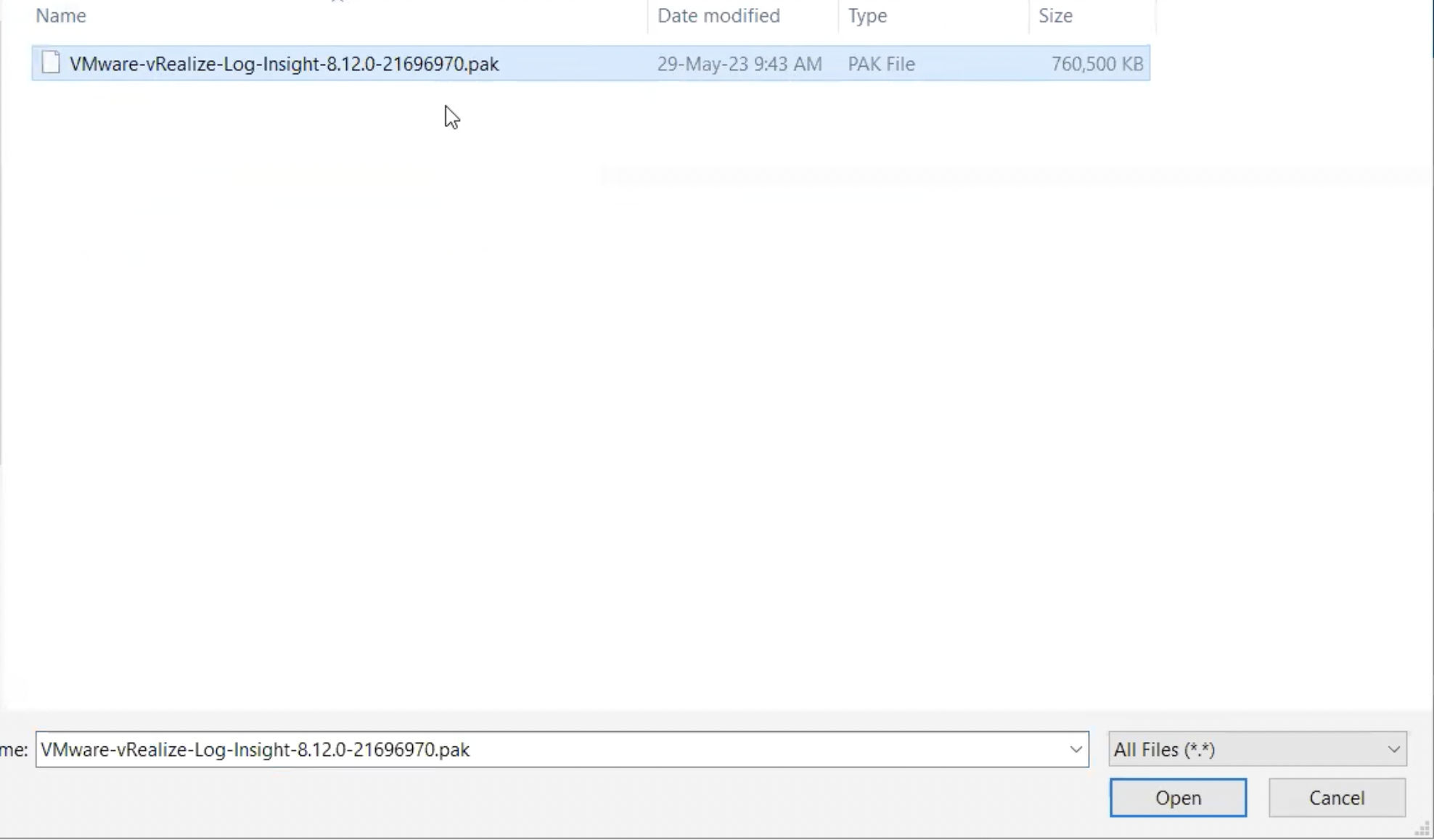
- VMware Aria Operations for Logs 8.12 – Upgrade Package
- VMware-vRealize-Log-Insight-8.12.0-21696970.pak
- File size: 742.68 MB
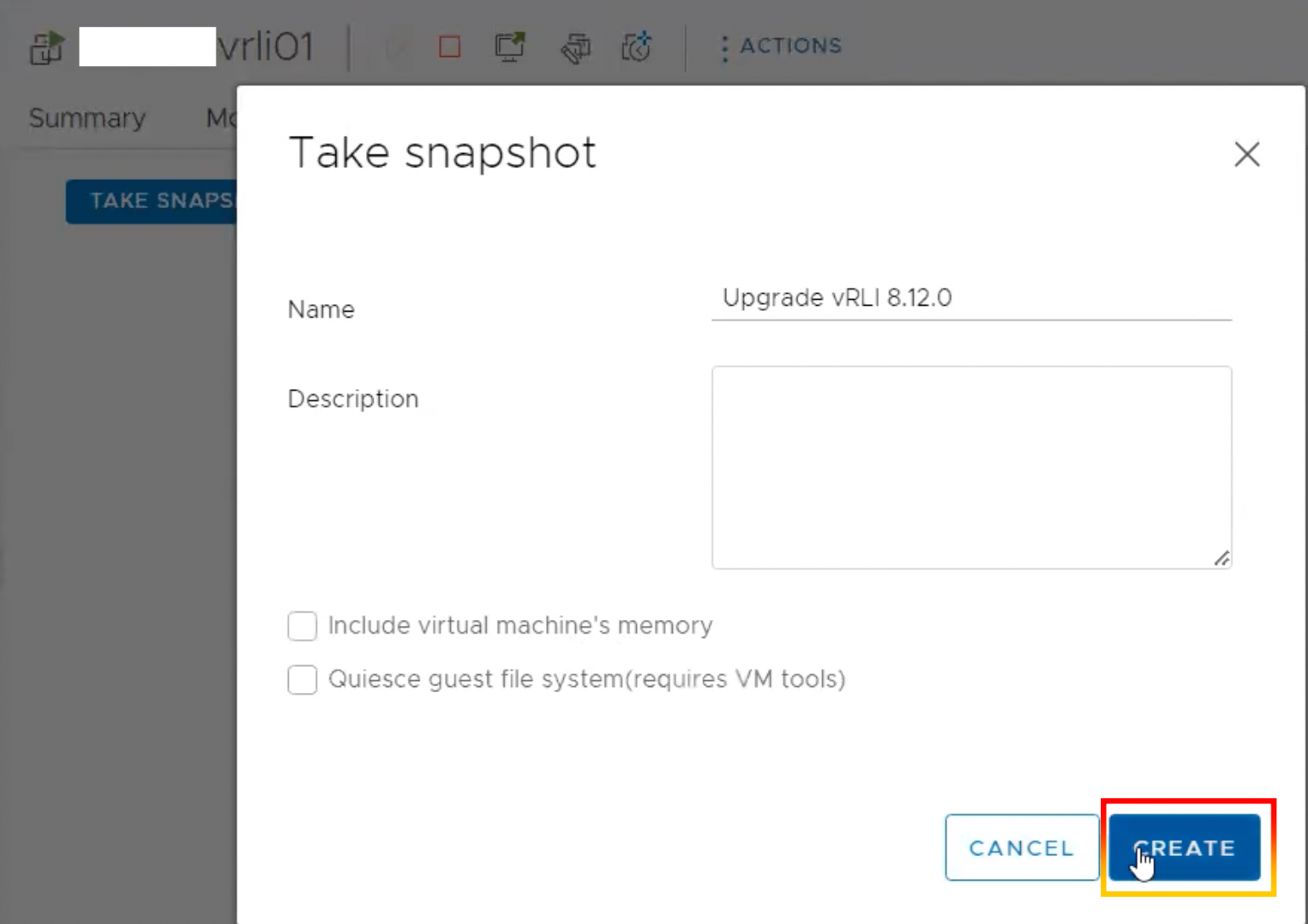
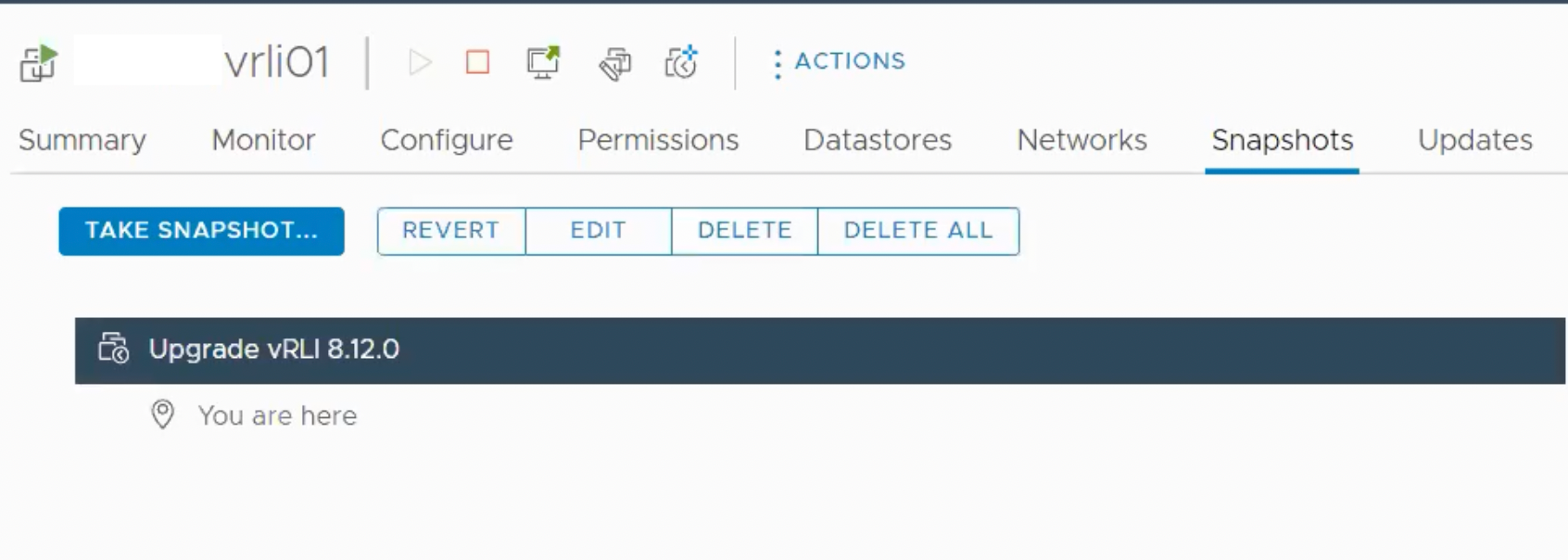
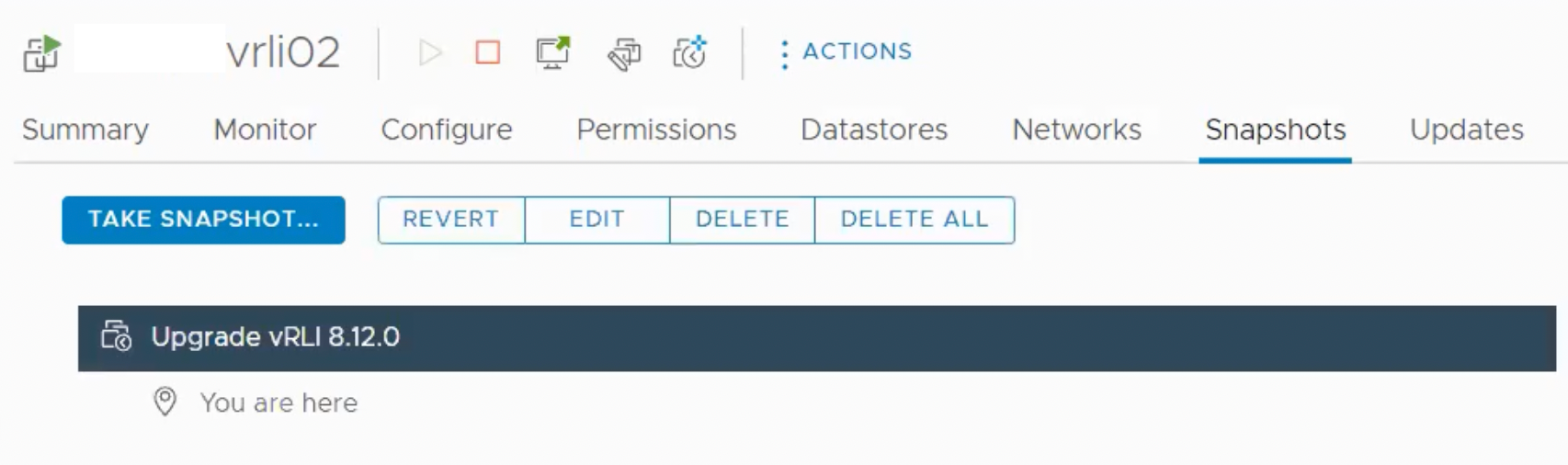
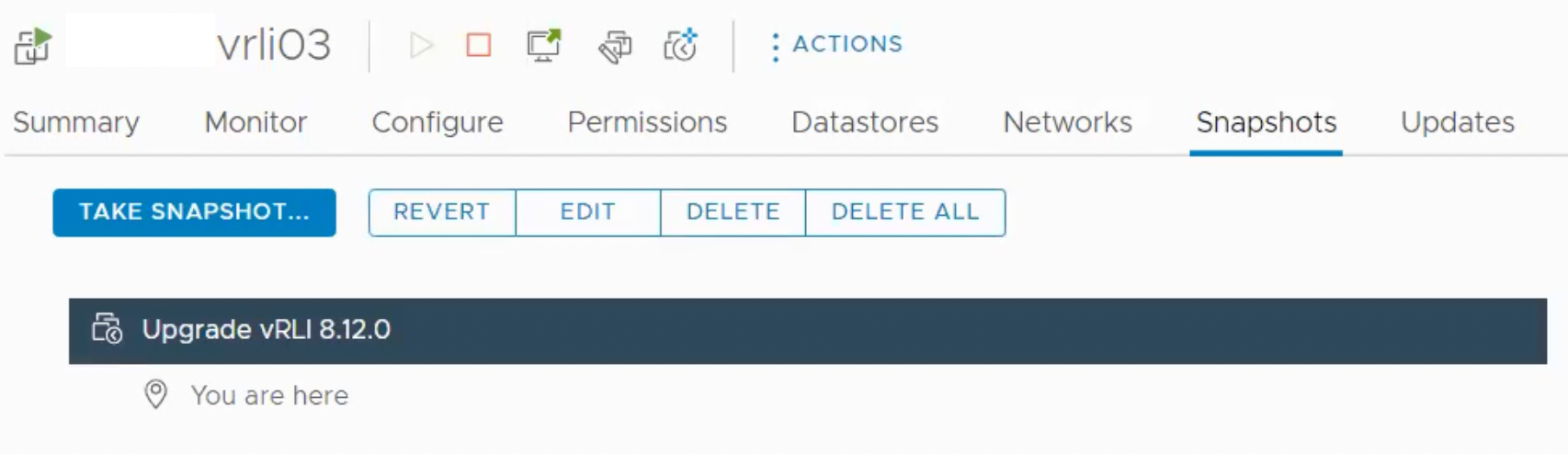
2.Take a snapshot of three nodes in VMware Aria Operations for Logs.
3.Log in to VMware Aria Operations and navigate to “Configuration” and “Cluster“.
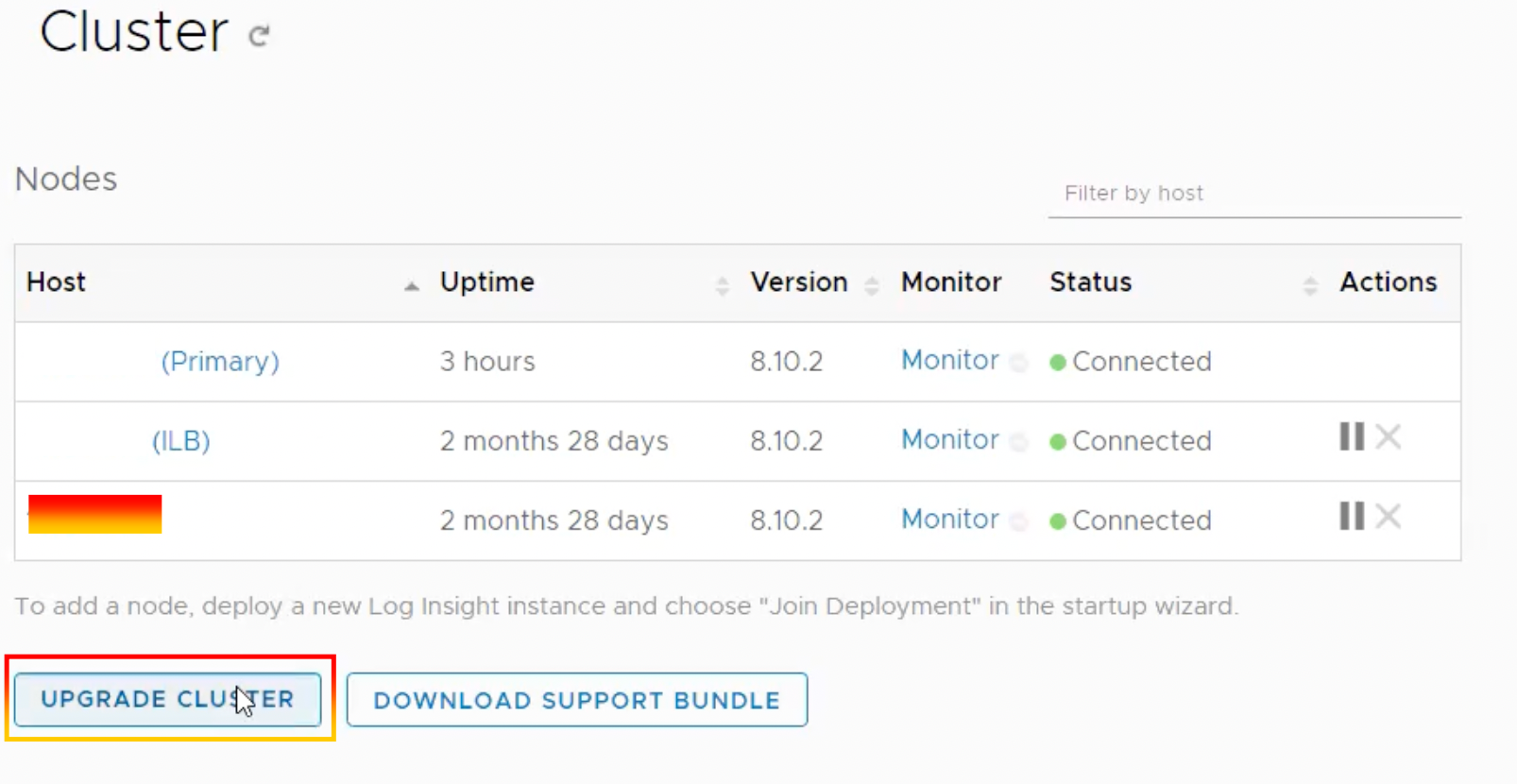
4.Select “UPGRADE CLUSTER“.
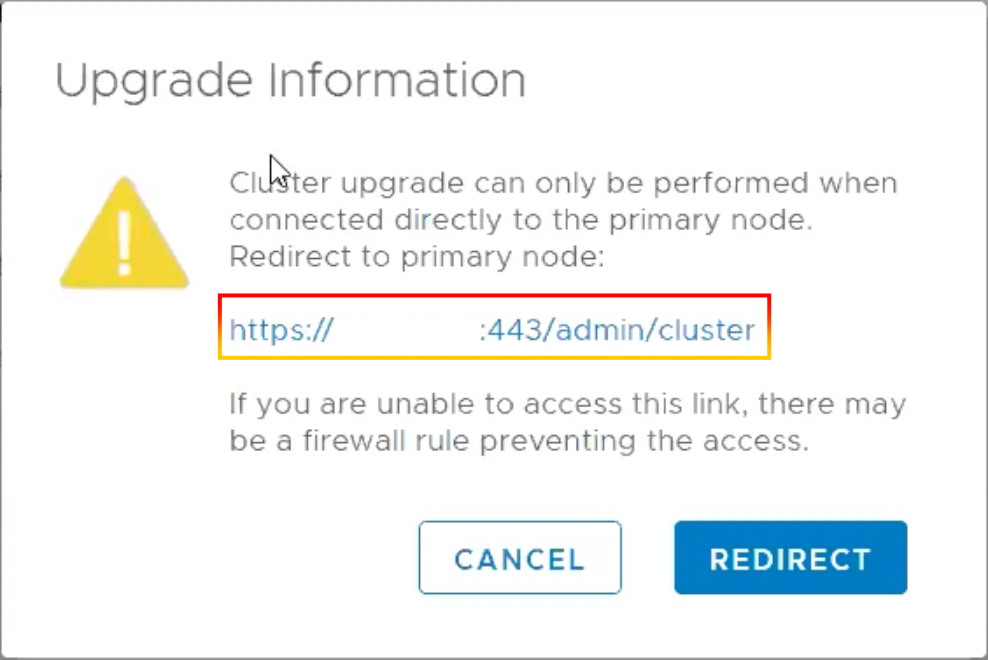
5.Cluster upgrade can only be performed when connected directly to the primary node.
6. You may navigate to “Configuration” and “Cluster” on the primary node, then click “UPGRADE CLUSTER” and choose an upgrade file..
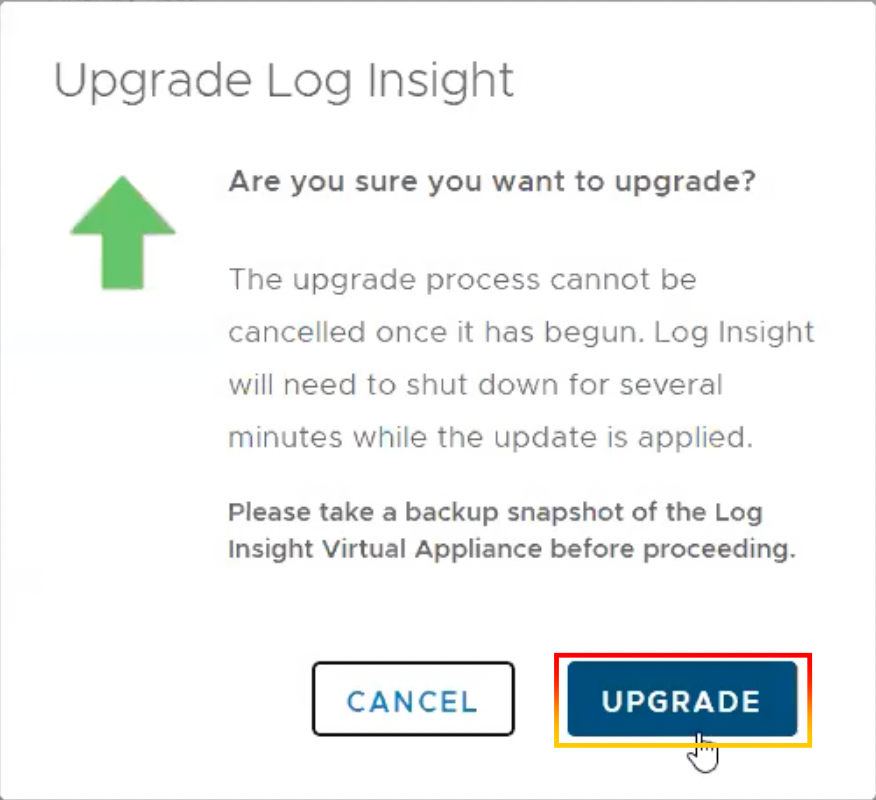
7.Click “UPGRADE“
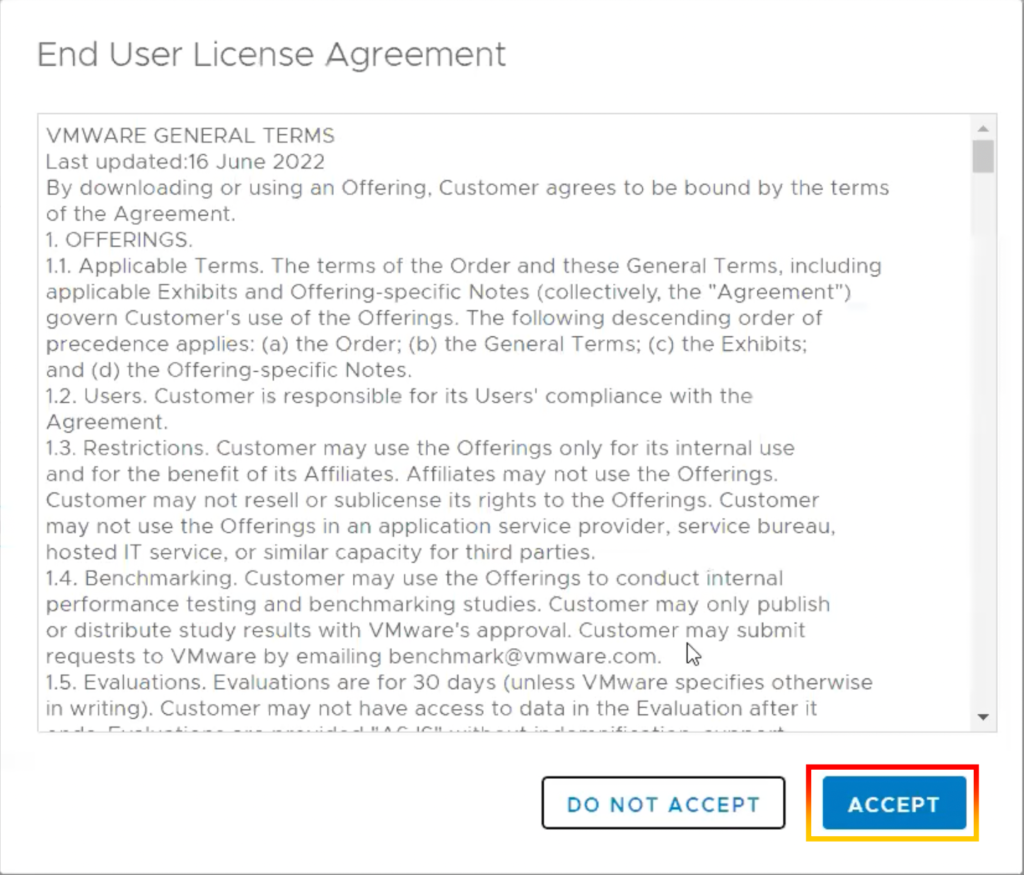
8.Click “ACCEPT“.
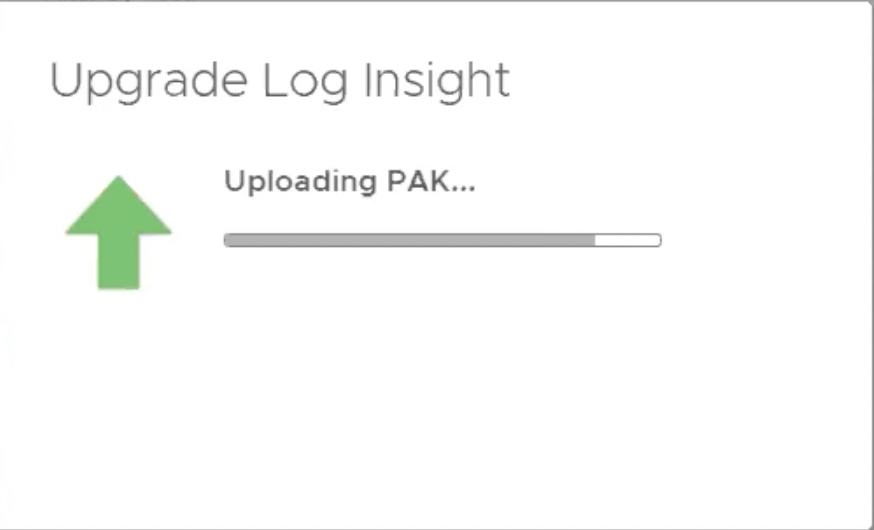
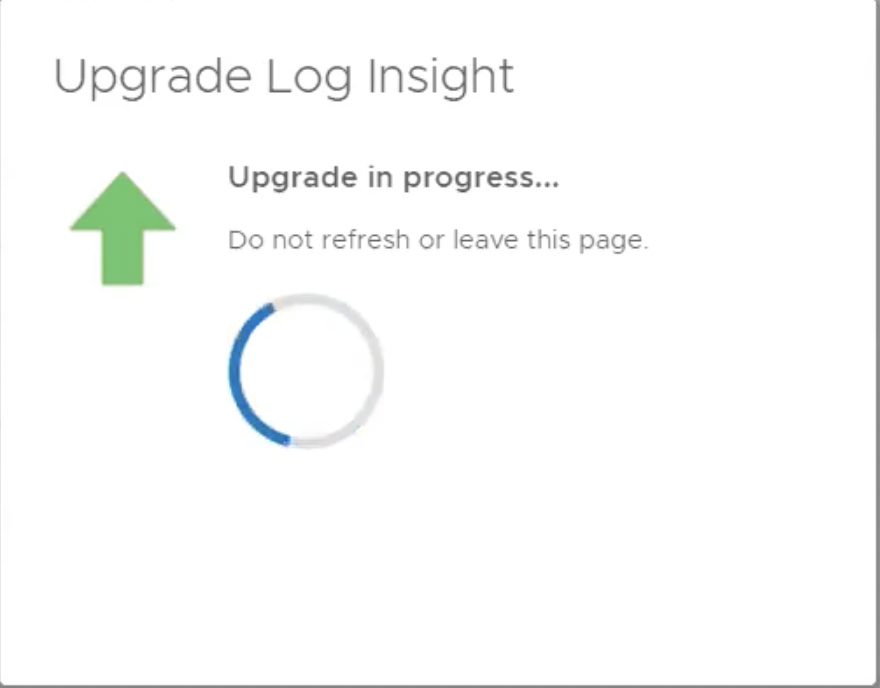
9.Upgrade Log Insight is now progress. (Do not refresh or leave this page)
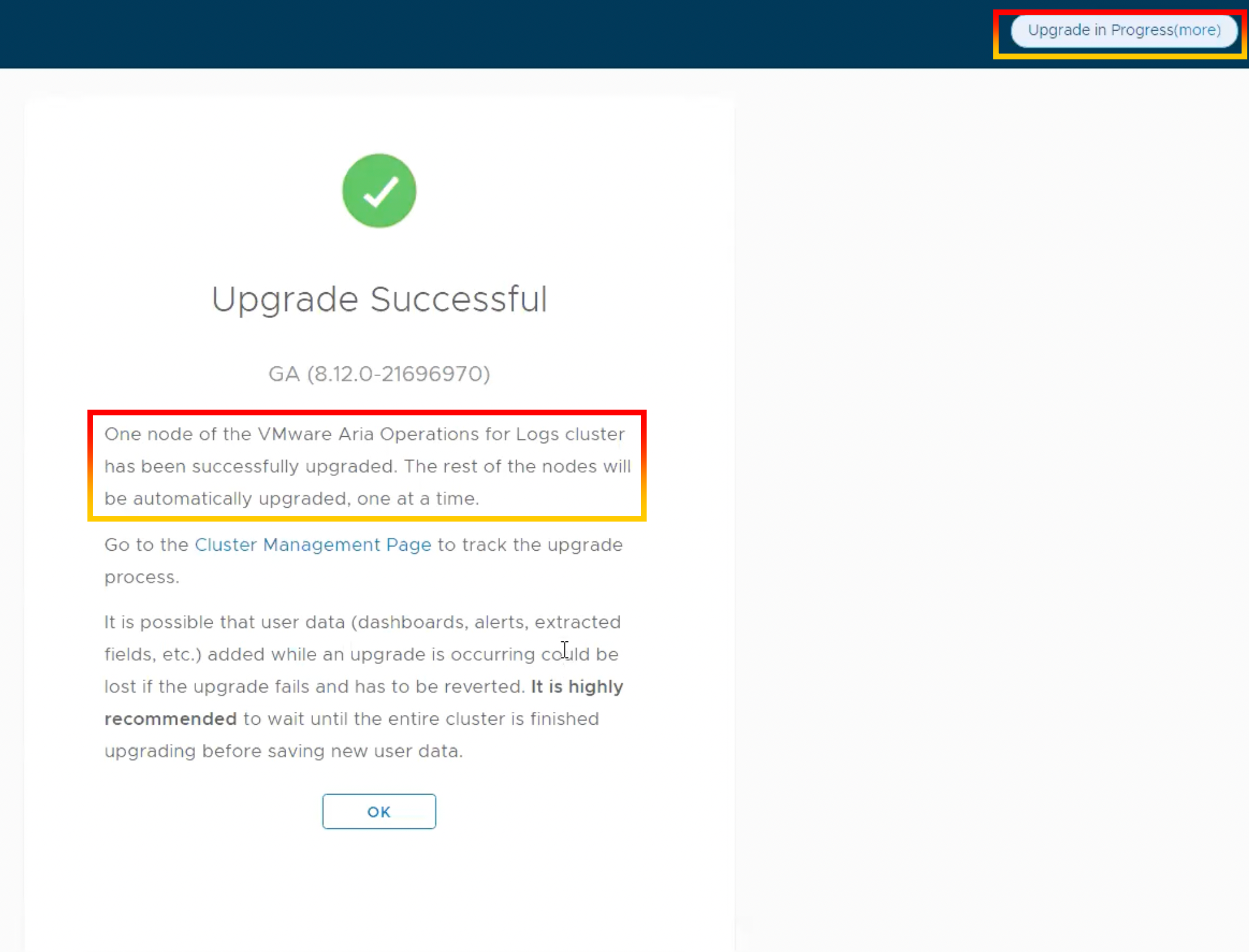
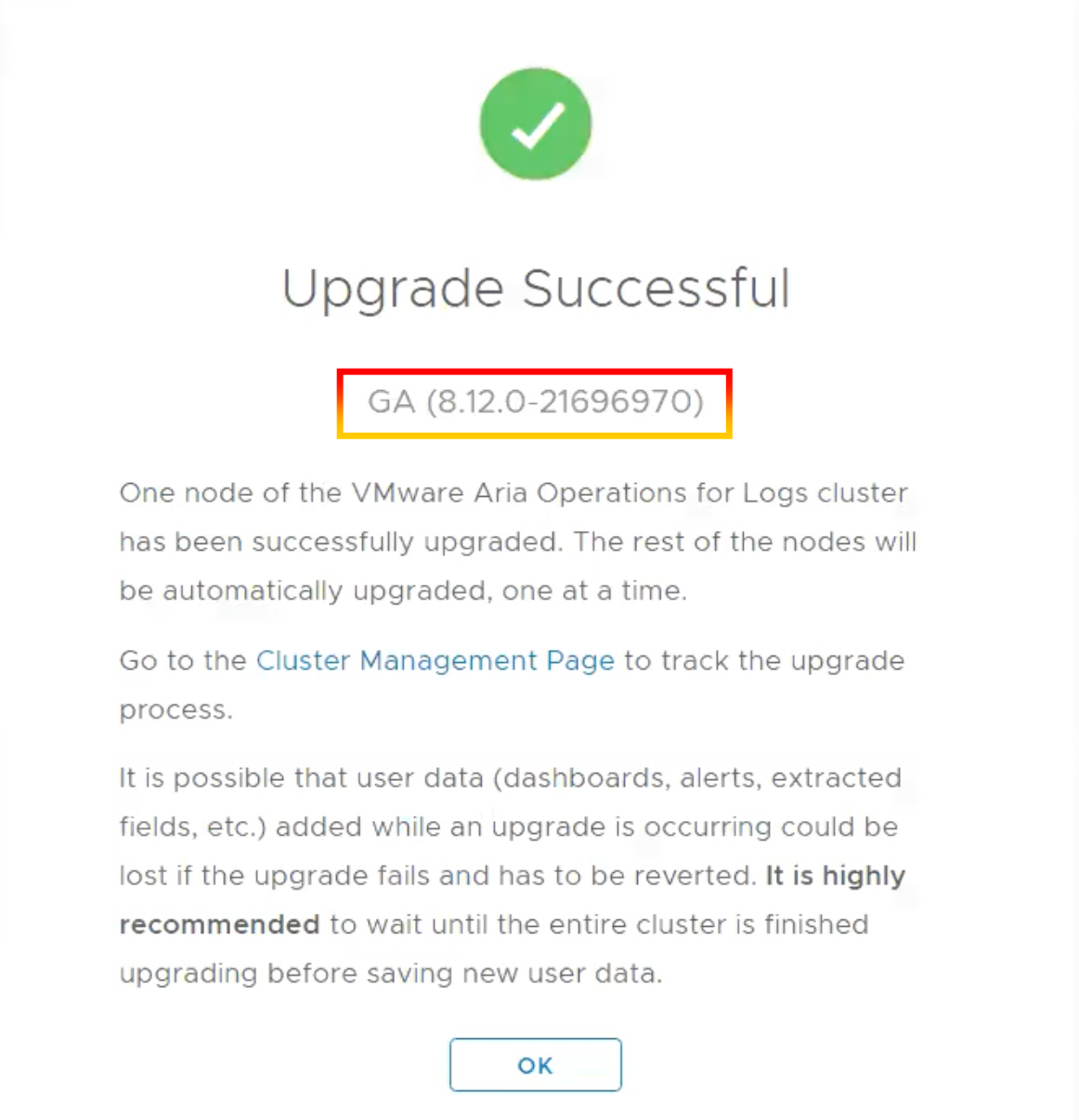
10.One node of the VMware Aria Operations for Logs cluster has been successfully upgraded.
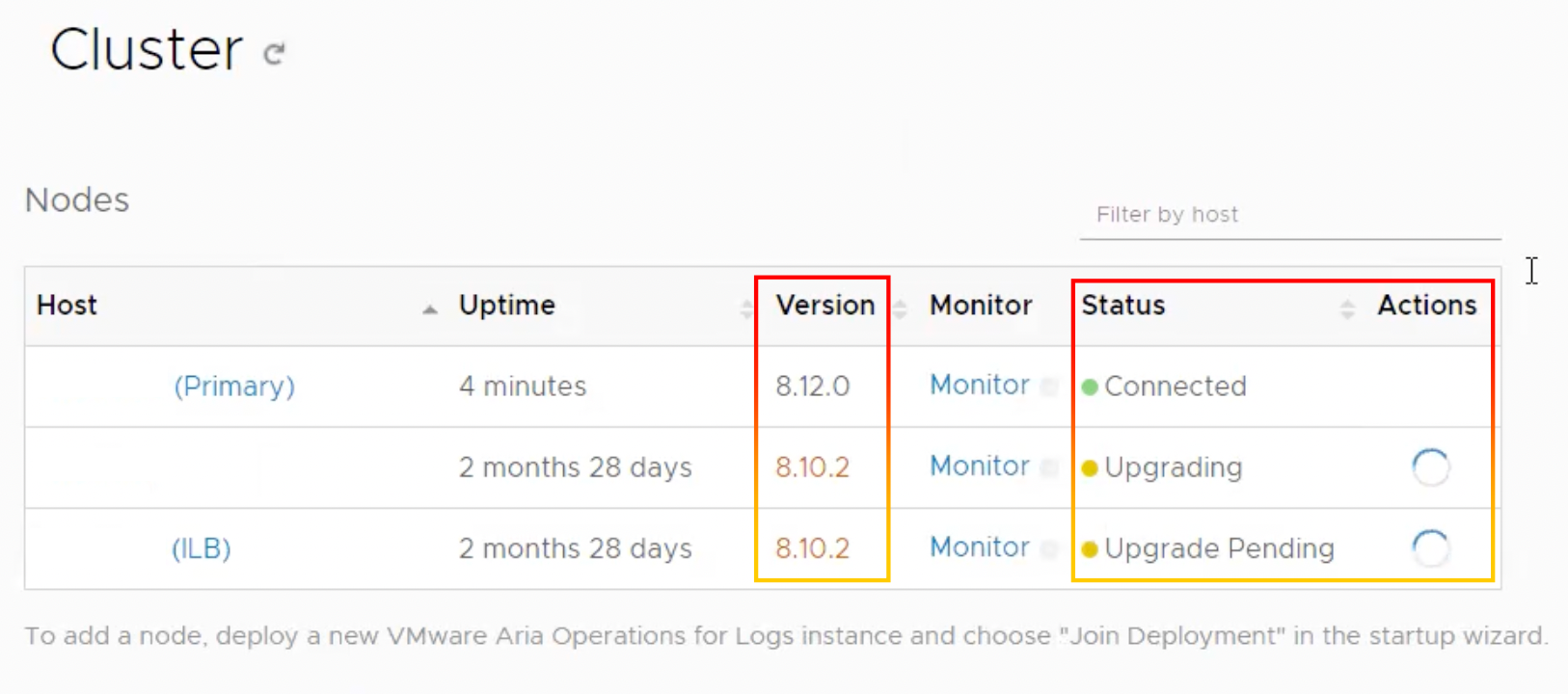
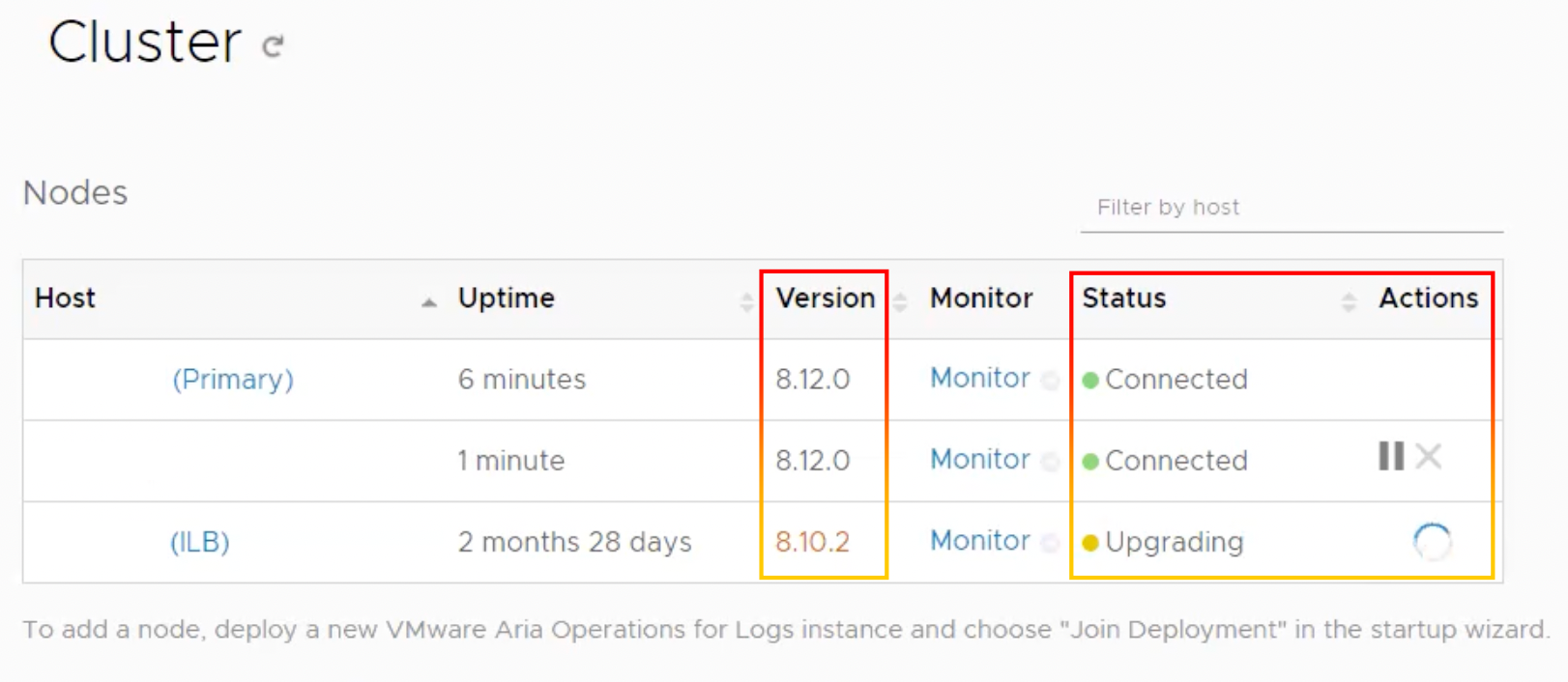
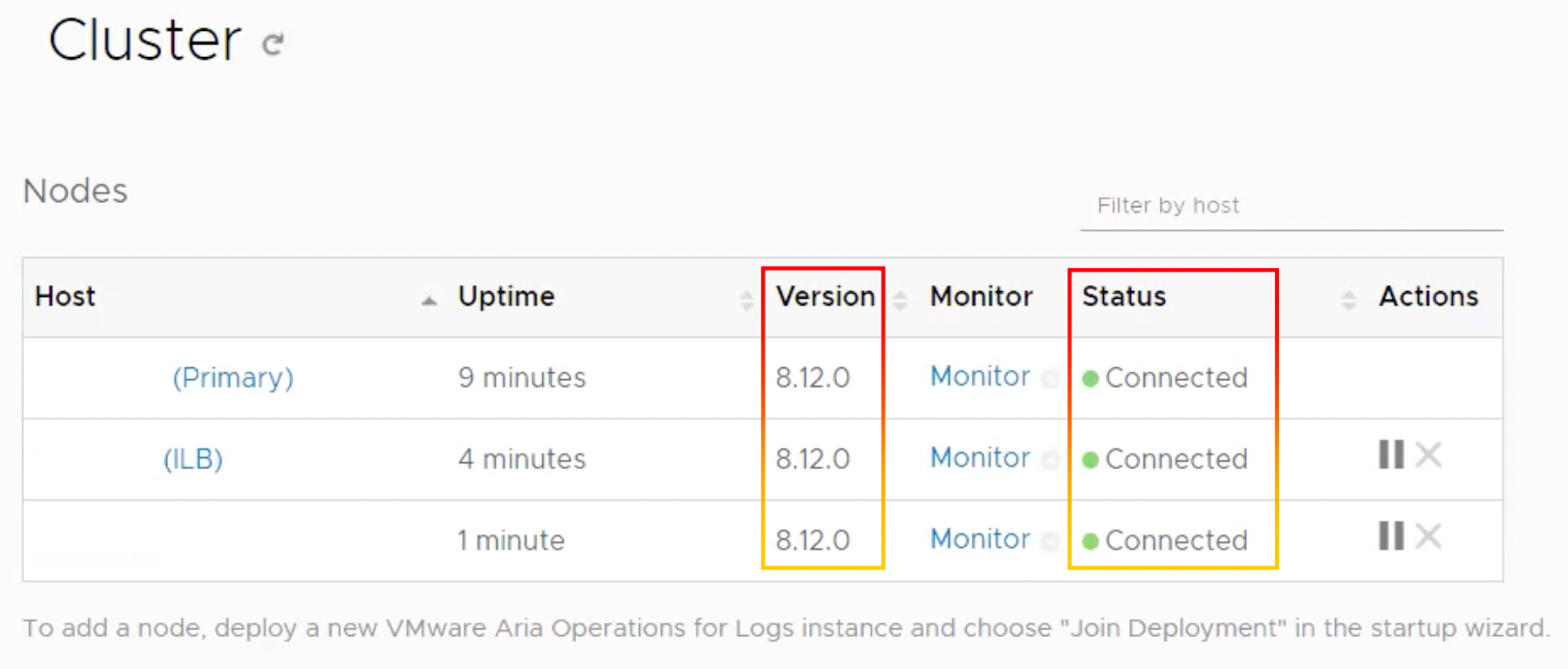
11.Log in to VMware Aria Operations for Logs master node to verify upgrade status.
- Node 1 has been completed.
- Node 2 has been completed.
- Node 3 has been completed.
12.VMware Aria Operations for Logs has been updated successfully
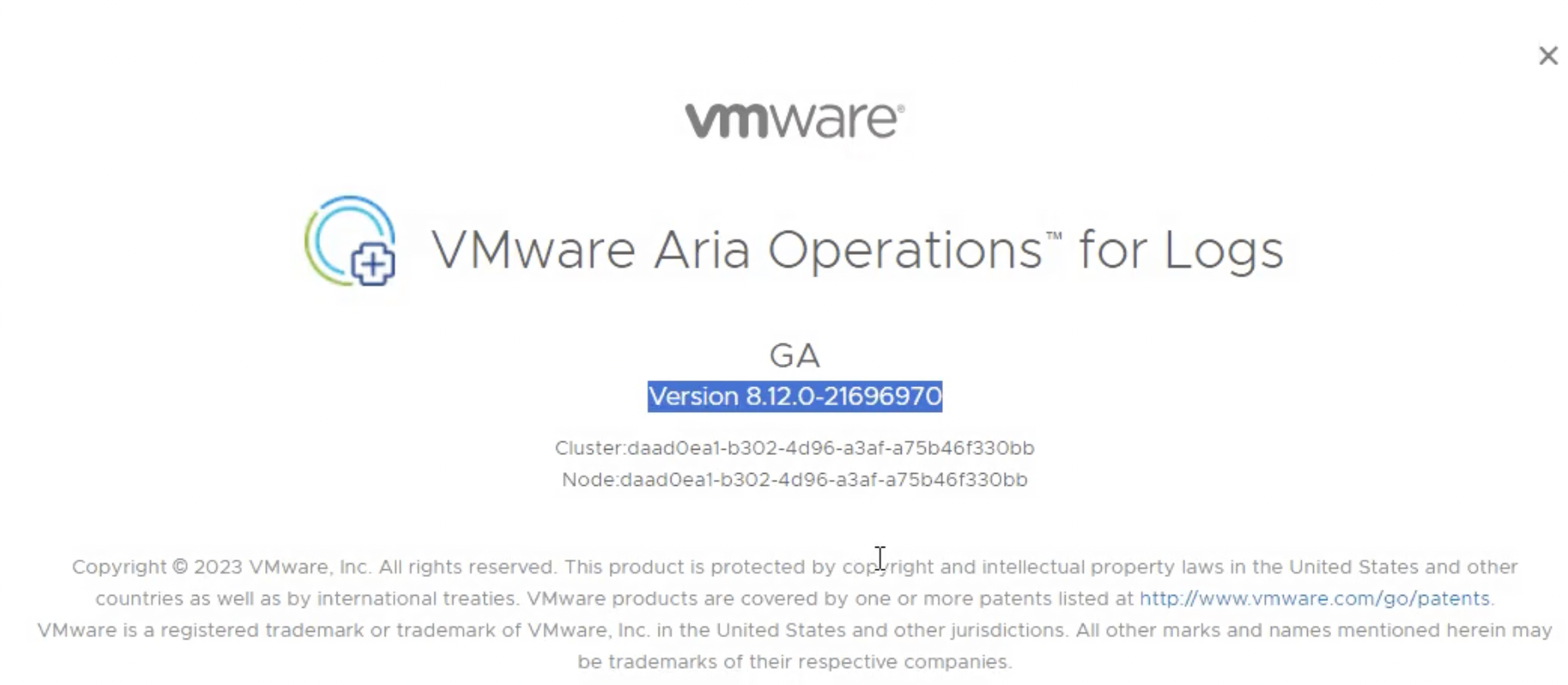
13.Log in to VMware Aria Operations to verify the version.
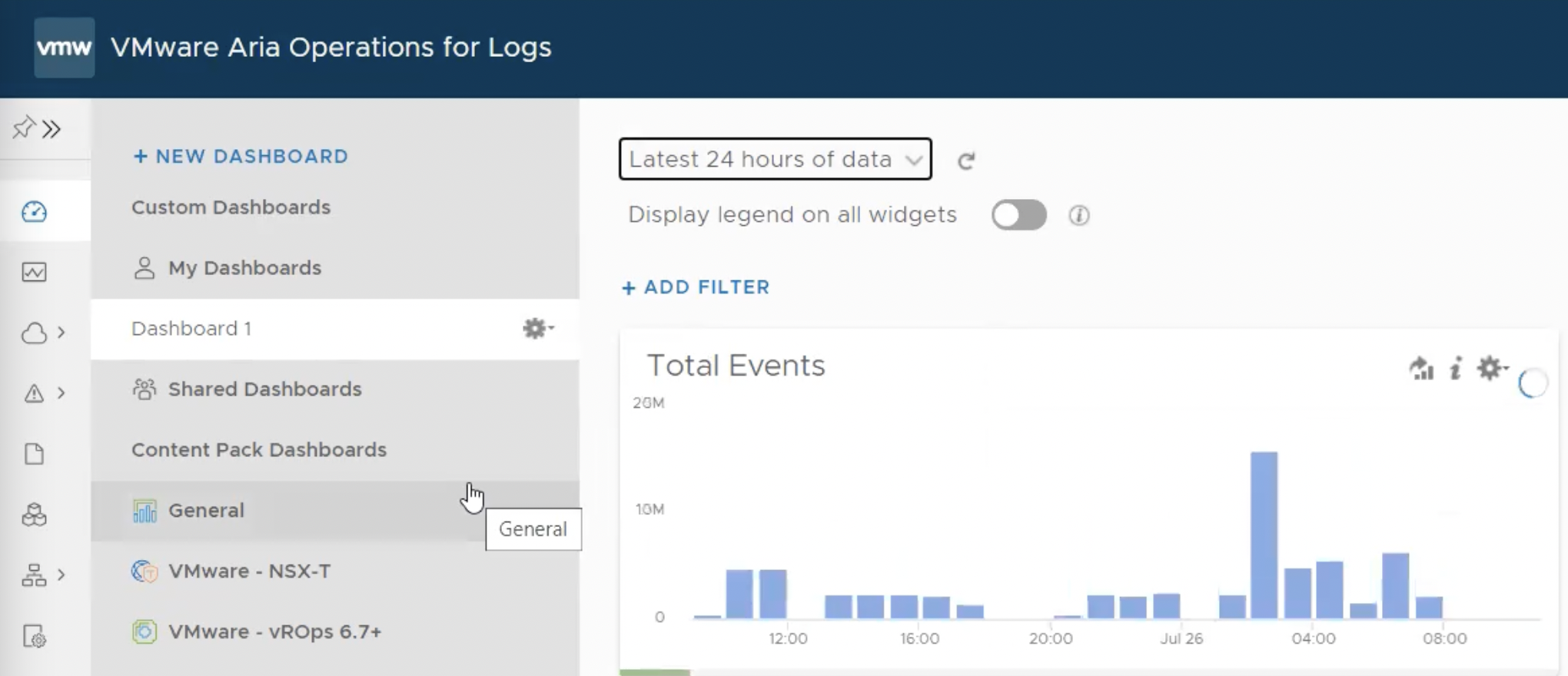
14.Check the dashboard and additional integrations.
Reference
https://www.vmware.com/security/advisories/VMSA-2023-0007.html
https://docs.vmware.com/en/VMware-Aria-Operations-for-Logs/8.12/rn/vmware-aria-operations-for-logs-812-release-notes/index.html
https://blogs.vmware.com/management/2023/04/whats-new-in-aria-operations-for-logs-8-12.html